MANAGED SECURITY SERVICES
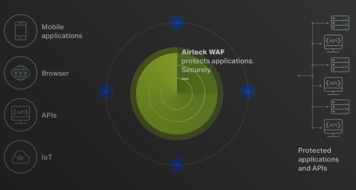
We protect your data and applications from physical and network attacks with a range of managed services.
On-premise DDoS mitigation, WAF and IAM as a service, regular vulnerability scans, server- and host-based IDS to monitor network traffic for suspicious or malicious activity, and reliable backup/restore in place - we ensure the security of your data and the high availability of your applications with a range of reliable protection measures.
Your applications run in their own dedicated network zones with their own set of rules. The level of security is determined by you. We work with you to develop a business continuity plan that is tailored to your needs.
Protect your IT systems with our Managed Security Services:
Protecting and securing your systems is a priority.
Talk to us about your requirements and send us your specifications. We will be happy to offer you a suitable service package.